Set Password Policies
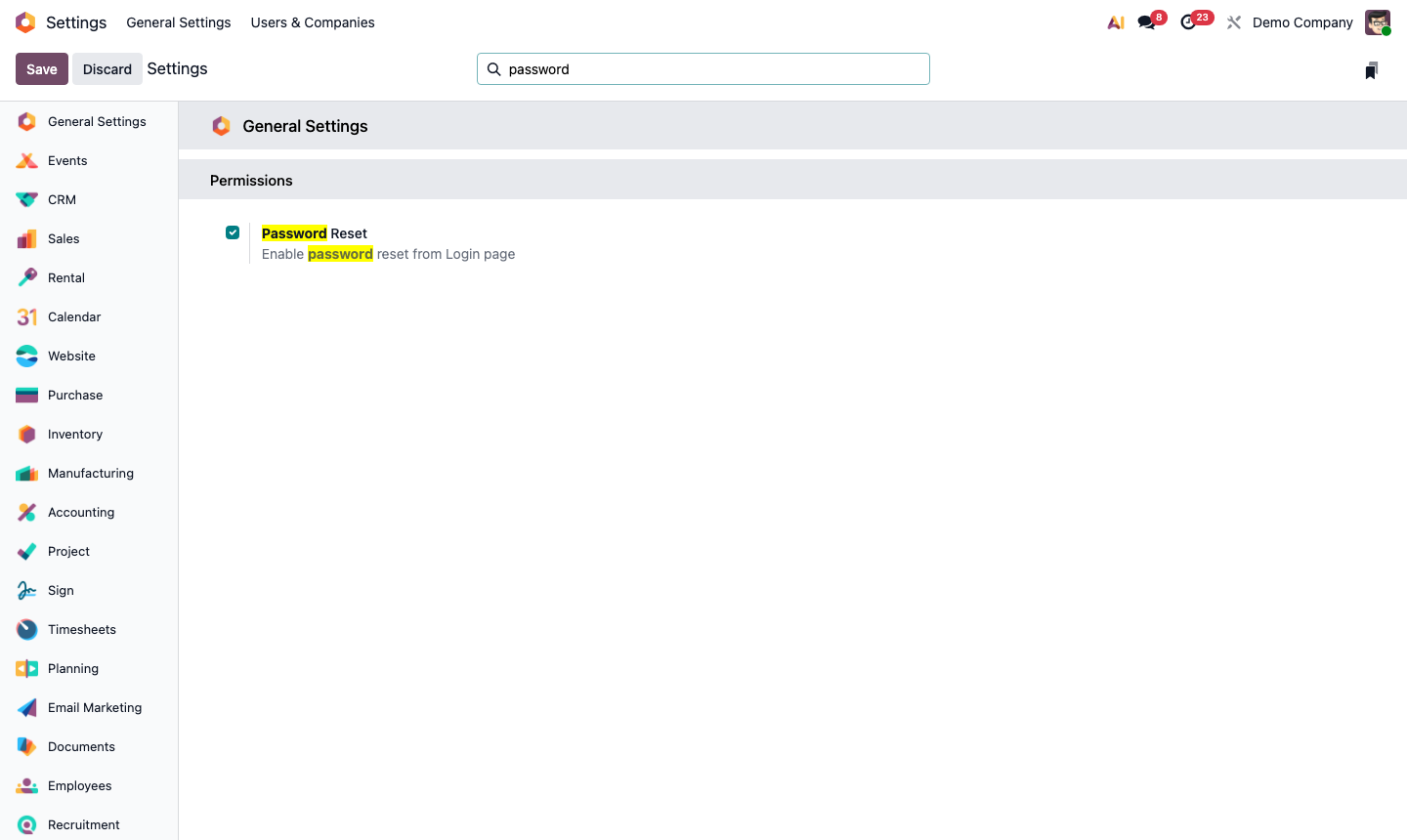
Go to Settings → Permissions (or search “Password” in Settings).
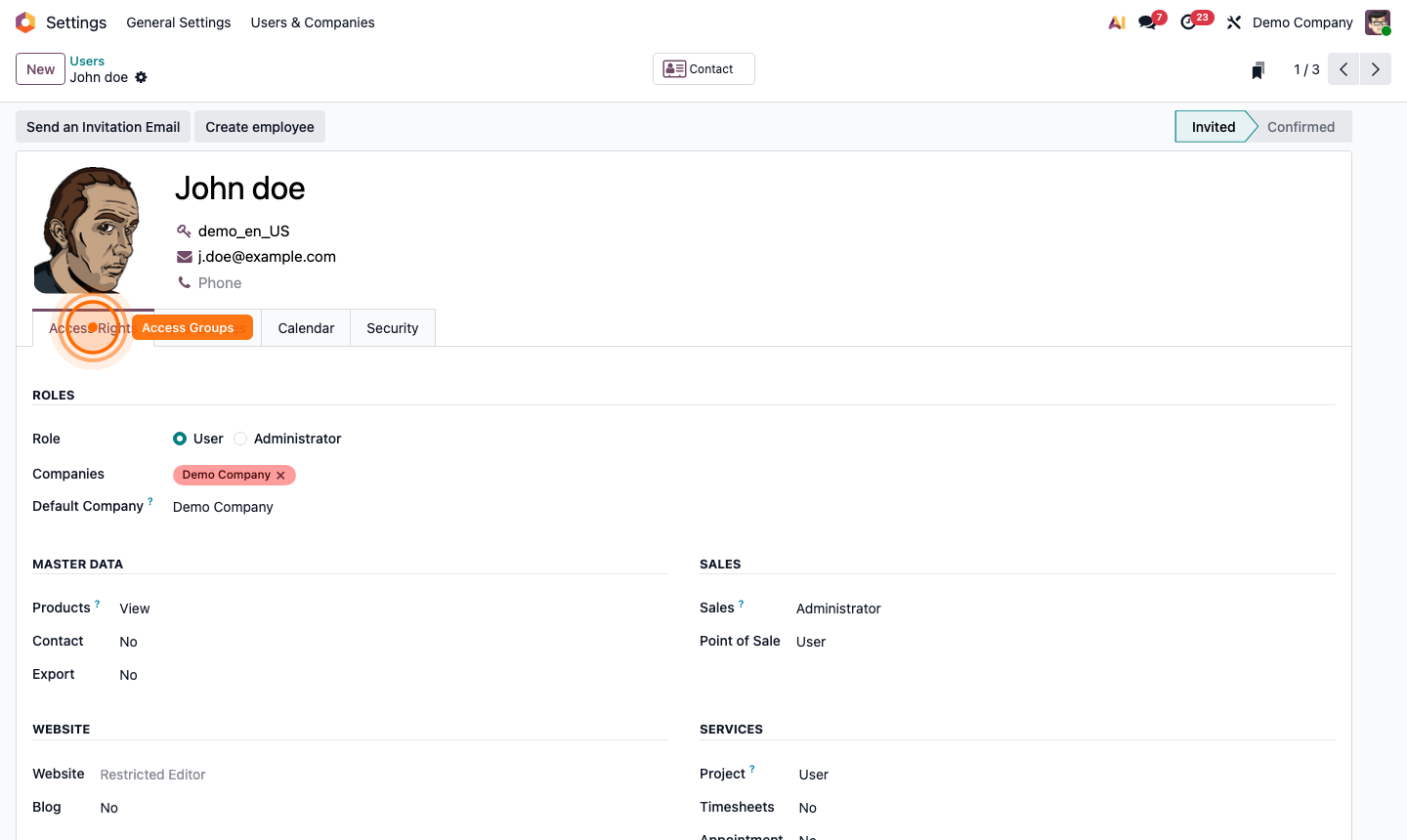
Configure:
- Minimum Password Length — recommended 10+ characters
- Password Reset — allow users to reset via email, or require admin action
- Session Expiry — how long before inactive sessions are logged out (e.g., 1 week)
For higher security environments, enable Lock Account After Failed Attempts to prevent brute-force logins.